On April 7, 2014 the OpenSSL Project released an update to address a critical vulnerability known as Heartbleed (CVE-2014-0160). This vulnerability, which affects multiple sites across the Internet, could be remotely exploited to leak sensitive information.
Action by New Relic
New Relic has reviewed all of our sites and applications, and we have determined that the majority of our sites, including www.newrelic.com, rpm.newrelic.com, and insights.newrelic.com are not vulnerable to this issue. New Relic did discover that the Documentation site (docs.newrelic.com) was vulnerable. This has now been patched, and the SSL certificate has been replaced.
Change your password
New Relic has no evidence that any customer data (including user names and passwords) was exposed. However, if you have any concerns about your account's protection, you should change your password.
This procedure is for users who sign in directly to APM and do not have partner accounts or SAML SSO enabled accounts:
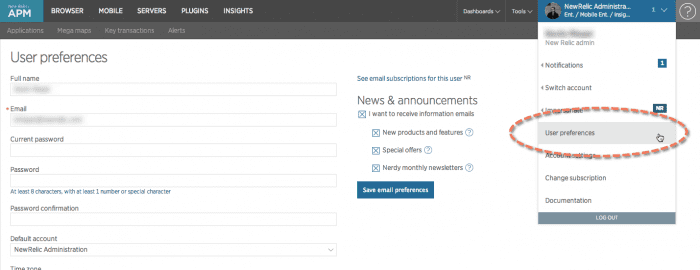
- Go to rpm.newrelic.com > (account dropdown) > User preferences.
- Type your Current password.
- Type your new Password (meeting minimum requirements), and then re-type the new password in Password confirmation.
- Select Save user preferences.
- Regenerate your API key.
rpm.newrelic.com > (account dropdown) > User preferences: Anyone can change their own New Relic user name, account email, password, and other settings.
For more help
If you need more help, check out these support and learning resources:
- Browse the Explorers Hub to get help from the community and join in discussions.
- Find answers on our sites and learn how to use our support portal.
- Run New Relic Diagnostics, our troubleshooting tool for Linux, Windows, and macOS.
- Review New Relic's and and documentation.